Does your employee listening program make your workers feel heard?
Internal Communication Software Security: Key Risks and Best Practices for 2026
April 22nd 2026
Internal communications used to be simple: a printed memo on a bulletin board or a town hall meeting in the cafeteria. Today, it’s a sprawling digital ecosystem of instant messaging, intranets, mobile apps, and video conferencing.
For modern businesses, this shift has been a game-changer. Real-time tools allow team members to collaborate across time zones, share sensitive information instantly, and maintain company culture in a remote work environment.
But this speed comes with a hidden cost: vulnerability.
As organizations rush to adopt new internal communication tools, security often takes a backseat to convenience. The result? Your internal channels – often trusted implicitly by employees – become the perfect entry point for attackers. From human error leading to data breaches to the rise of shadow IT, the risks are real and growing.
In this guide, we explore why your internal channels are a growing target, the common risks you face, and the must-have security features you need to protect your organization without sacrificing employee engagement.
Why internal communication is a growing risk
For years, cybersecurity focused heavily on hardening the perimeter – protecting the company from external threats like email phishing and firewall breaches. But in the modern hybrid work era, the perimeter has dissolved.
Internal communication tools have become the soft underbelly of enterprise security. Here’s why the risk landscape has shifted so dramatically.
Internal messages are trusted more than email
Employees are trained to be suspicious of external emails. However, when a message pops up on an internal messaging platform or intranet, their guard goes down.
If an attacker compromises a colleague's account, a simple message like "Hey, check this doc" bypasses skepticism. This implicit trust makes internal phishing attempts significantly more successful than traditional methods.
Remote work creates unsecured entry points
Team members are no longer sitting behind a secure corporate firewall. They’re accessing sensitive data from coffee shops, airports, and home networks.
If your employee communication software lacks robust mobile app security or multi-factor authentication (MFA), every personal device becomes a potential entry point for unauthorized access.
Internal channels hold your most sensitive data
We often think of internal comms as "just chat." In reality, these channels are a repository of your organization's most sensitive information. From product roadmaps and customer lists to passwords shared in private channels, your internal communication tools hold the keys to the kingdom.
A breach here doesn't just leak conversations; it leaks intellectual property.
Unapproved apps create security blind spots
When official tools are clunky or difficult to use, employees find workarounds. They create WhatsApp groups or use personal messaging apps to share files because it’s faster.
This shadow IT is invisible to the IT team, meaning data breaches can happen without anyone knowing until it is too late. The rigorous security of your official tech stack effectively becomes useless if no one is using it.
7 common internal communication security threats
To protect your organization, you first need to identify the threats. Unlike external attacks which often target infrastructure, internal communication risks typically target human error and convenience.
Here are the seven most common vulnerabilities facing modern businesses today.
1. Shadow IT and consumer apps
This is arguably the biggest risk for most organizations. When employees find official software difficult to use, they switch to consumer messaging apps like WhatsApp or Facebook Messenger to share sensitive data.
These apps lack enterprise oversight, data retention policies, and compliance controls. If an employee leaves the company, your data leaves on their personal phone.
2. Account compromise via phishing
Attackers have shifted focus from email to internal channels.
If a hacker gains unauthorized access to one employee's Slack or Teams account, they can send phishing links to the rest of the company from a trusted source.
Because employees inherently trust internal messages, they are far more likely to click.
3. Weak access controls
Many organizations suffer from permission creep, where employees retain access to projects or channels they no longer need.
Without strict role-based access control (RBAC), a junior employee – or a compromised account – might have access to executive-level financial data or HR records simply because no one restricted the permissions.
4. Accidental data leaks
Not all threats are malicious; many are just mistakes.
The speed of instant messaging leads to errors – like pasting a confidential client list into a public channel or sharing a link with "Anyone with the link" permissions instead of "Internal only."
In a fast-paced environment, these slip-ups happen daily.
5. Insider threats
These can be malicious (a disgruntled employee downloading customer lists before quitting) or unintentional (a well-meaning employee uploading sensitive files to a public AI tool to summarize them).
Without monitoring or data loss prevention (DLP tools), these internal actions go unnoticed until the damage is done.
6. Metadata leakage
Even if the content of your messages is encrypted, the metadata – who’s talking to whom, and when – can reveal sensitive information.
For example, a sudden spike in messages between the CEO and a bankruptcy lawyer reveals a lot, even if you can't read the text. Many standard tools fail to obfuscate this communication pattern data.
7. Regulatory exposure
For regulated industries, internal communication is a legal record. Failing to archive messages correctly, or allowing employees to delete chats that should be retained, can lead to massive fines under GDPR, HIPAA, or financial regulations.
Using non-compliant tools creates a significant legal blind spot.
Must-have security features in internal communication platforms
Policy alone cannot stop a breach. You need technology that enforces security automatically. When evaluating internal communication solutions, do not compromise on these six technical capabilities.
End-to-end encryption (E2EE)
Encryption is non-negotiable. Look for software solutions that offer end-to-end encryption for both messages and file transfers.
This ensures that even if data is intercepted on a public Wi-Fi network, it remains unreadable to anyone but the intended recipient.
Single sign-on (SSO) integration
Passwords are the weakest link in security. Your platform must support single sign-on (SSO) (e.g., via Okta or Microsoft Azure).
This allows employees to log in using their existing corporate credentials, eliminating password fatigue and ensuring that when an employee leaves, their access to company news and data is instantly revoked.
Role-based access control (RBAC)
Not every employee needs access to every document. Role-based access control allows you to define granular permissions based on an employee's job function.
This ensures that a frontline worker sees the schedule and safety updates, while sensitive financial reports are restricted to the executive leadership team.
ISO 27001 and SOC 2 certification
Trust, but verify. Any cloud-based vendor you choose must hold industry-standard security certifications like ISO 27001 and SOC 2 Type II.
These certifications prove that the vendor has rigorous physical and digital security controls in place to protect your data from data breaches.
Mobile device management (MDM) compatibility
Since employees will access the platform via mobile, the software must play nicely with your MDM tools. This allows IT to wipe the mobile app data remotely if a device is lost or stolen, without affecting the employee's personal photos or apps.
Automated data retention policies
Storing chat logs forever is a liability risk. Your software should allow you to automate data retention.
For example, you can set the system to automatically delete general chat logs after 90 days while archiving legal channels for 7 years, ensuring compliance with GDPR and other regulations.
Related reading → 7 Secure Intranet Software Vendors for Security-Focused IT Teams
Best practices for secure internal communication
Buying secure software is only half the battle. To truly protect your organization, you need to combine the right tools with the right behaviors. Even the most encrypted platform can be compromised by human error.
Here are five best practices to build a resilient internal communication strategy.
Mandate multi-factor authentication (MFA)
Weak passwords are the primary cause of unauthorized access. You should enforce multi-factor authentication (MFA) for every single user, without exception.
This ensures that even if an employee’s password is stolen via phishing, the attacker cannot access the system without the second verification step (like a code on a mobile phone).
Establish clear data governance policies
Do your employees know what they can and cannot share on chat? Create a clear policy that categorizes sensitive information.
Green: Public company news, social updates, and general questions.
Red: Customer PII, passwords, and financial data (Forbidden on chat; must be shared via secure file sharing tools). By clarifying these rules, you reduce accidental data breaches caused by confusion.
Conduct regular security awareness training
Your employees are your first line of defense. Regular training sessions should teach team members how to spot CEO fraud (impersonation attempts) and suspicious links within messaging tools.
Make security training part of onboarding so new hires understand the risks of shadow IT from day one.
Automate software updates
Outdated software is a playground for hackers. Ensure that your internal communication tools are set to automate updates.
Cloud-based platforms typically handle this for you, patching vulnerabilities instantly without requiring manual intervention from your IT team.
Conduct quarterly access reviews
People change roles, but their permissions often don't. Schedule quarterly reviews to audit who has access to what. If an employee has moved from Finance to Marketing, their access to sensitive data in financial channels should be revoked immediately to adhere to the principle of least privilege.
Related reading → Intranet Security Best Practices, Threats & Solutions
Why usability = security
There is a dangerous myth in the corporate world that "secure" means "complex."
IT teams often lock down systems so tightly – requiring VPNs, complex logins, and clunky interfaces—that the software becomes painful to use. When this happens, security backfires. Frustrated employees will bypass your secure tools and switch to user-friendly consumer apps (like WhatsApp) to get their work done.
Therefore, the best security feature is a great employee experience.
- Streamlined workflows: When a platform integrates instant messaging, video, and files in one place, employees have no reason to leave the secure environment.
- Mobile accessibility: A well-designed mobile app encourages frontline staff to use official channels instead of unsecured text messages.
- Engagement: When employees enjoy using the platform for company culture and recognition, they naturally adopt it for business communication too.
To eliminate shadow IT, you don't need stricter policies; you need better software. You need a modern platform that is as easy to use as social media but as secure as a bank vault.
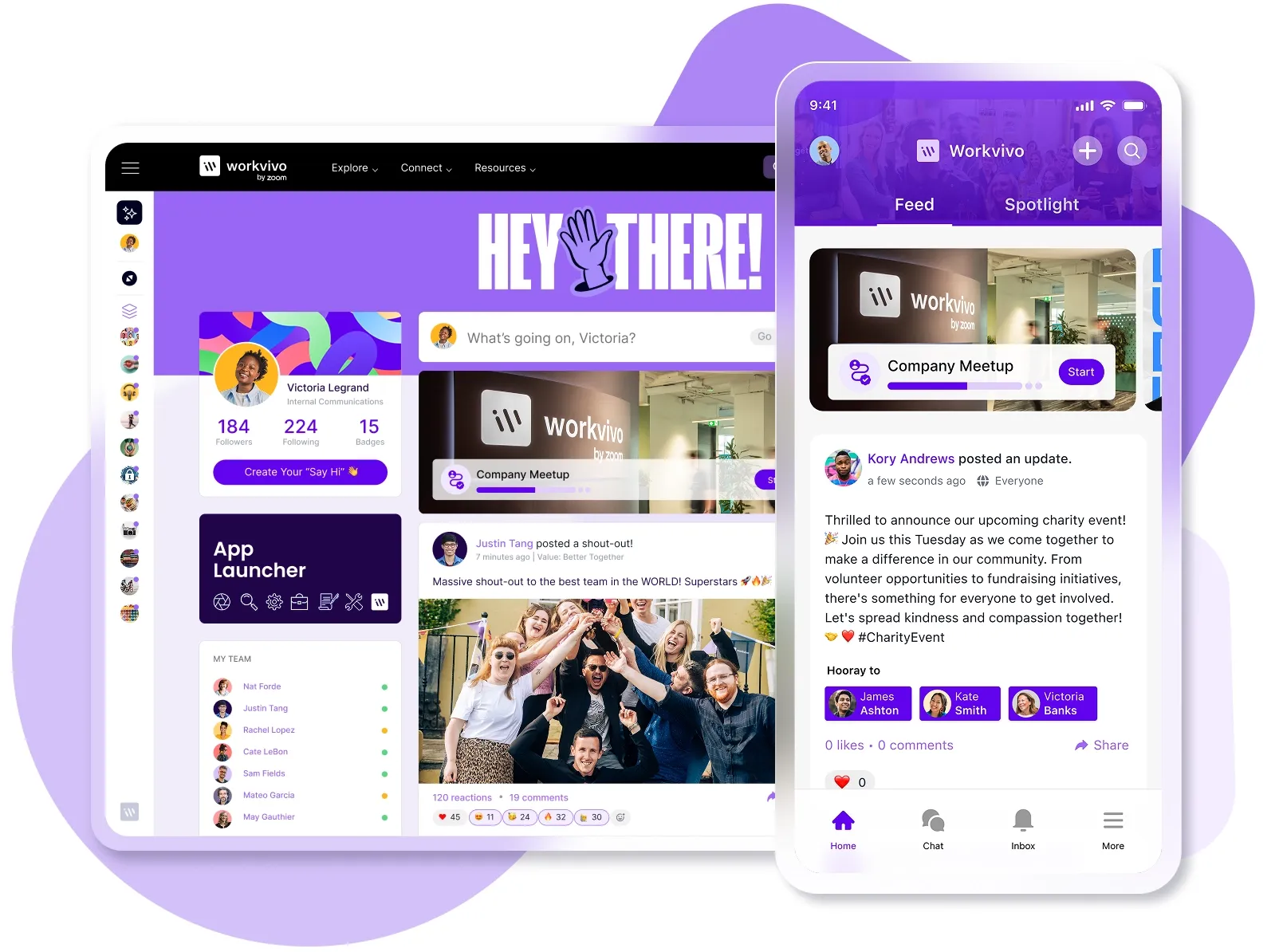
Workvivo: Enterprise-grade security without the complexity
Usually, there’s a trade-off: highly secure software is difficult to use, and easy-to-use software isn't secure. This is exactly what drives employees toward shadow IT.
Workvivo eliminates the compromise.
We built a platform that delights employees with a social, intuitive interface, while operating with the rigorous security controls demanded by the world's most regulated industries. It is the only platform that satisfies the CISO’s need for control and the employee’s need for connection.
Why leading enterprises trust their data with Workvivo:
- The gold standard of compliance: We don't just check the box. Workvivo is ISO 27001 certified and produces an annual SOC 2 Type 2 report. Our Information Security Management System (ISMS) is audited annually to ensure we meet the highest global standards.
- Trusted by the world's biggest brands: Security-conscious giants like Amazon, Virgin, Ryanair, and Bupa rely on Workvivo as their digital heart. They choose us because we prove that a secure platform doesn't have to be a silent one.
- Fortress-level infrastructure: Hosted on AWS, we leverage top-tier cloud security services protected by layered technical controls. We don't wait for threats to appear; we contract reputable third-party organizations to conduct regular penetration testing, ensuring our defenses are always ahead of the curve.
Secure your internal communications with the platform that protects your data and your culture. Book a demo today.
FAQs
Why are legacy intranets like SharePoint considered a security risk?
While SharePoint has backend security, its complexity often leads to human error. Permission creep is common, where sensitive folders are accidentally shared with the wrong groups because the settings are confusing.
A modern intranet solves this by centralizing internal communication channels and simplifying access controls, reducing the chance of accidental data exposure.
How does streamlining tools reduce security vulnerabilities?
When employees have to navigate disjointed collaboration tools and project management apps, they get frustrated and switch to unapproved consumer apps (like WhatsApp) to share files. By using a single communication system to streamline access, you keep employees inside the secure, monitored environment.
Is it safe to host employee recognition on a social feed?
It is safer than the alternative. Without a dedicated internal hub, employees often celebrate wins on public social media (LinkedIn/Facebook), inadvertently leaking trade secrets or client names. A secure platform allows for public employee recognition and detailed use cases to be shared, but keeps that data strictly behind your firewall.
What metrics should I track to improve security?
Security teams should track metrics related to adoption and reach. If usage of your official internal communication channels is low, it likely means employees are using insecure solutions.
High engagement on collaboration platforms is actually a strong indicator of a healthy, secure digital environment.
Discover more content on internal communications:
- What Is Internal Communications? The Complete Guide to Effective Employee Communication
- How to Create an Internal Communications Plan in 6 Steps
- Internal Communications Analytics: How to Measure What Matters
- How to Create an Effective Internal Communications Content Strategy
- Fixing the “Great Detachment”: How to Improve Employee Engagement through Internal Communication
- Internal Communication Software Cost: Pricing Models, Features, and What to Expect
- Simpplr Review for 2026: Pros, Cons, Features & Pricing
- Slack Pros and Cons for 2026 [And Better Alternatives]
- 15 Best Enterprise Collaboration Tools Reviewed for 2026
- 10 Essential Internal Communication Channels to Optimize This Year
- How to Set Practical Internal Communications Goals [with Examples]
- The Ideal Internal Communications Team Structure for 2026
- Internal Communications Benchmarks for 2026: How Does Your Internal Comms Strategy Stack Up?
- Internal vs External Communication: What's the Difference?
- 12 Benefits of Internal Communication in the Workplace
- How to Build a Great Internal Communications Dashboard [Key Functionalities, Metrics to Include & Examples]
- The Top 11 Benefits of Unified Communication Platforms
- Internal Communication Software Security: Key Risks and Best Practices for 2026